A switched chaotic encryption scheme using multi-mode generalized modified transition map
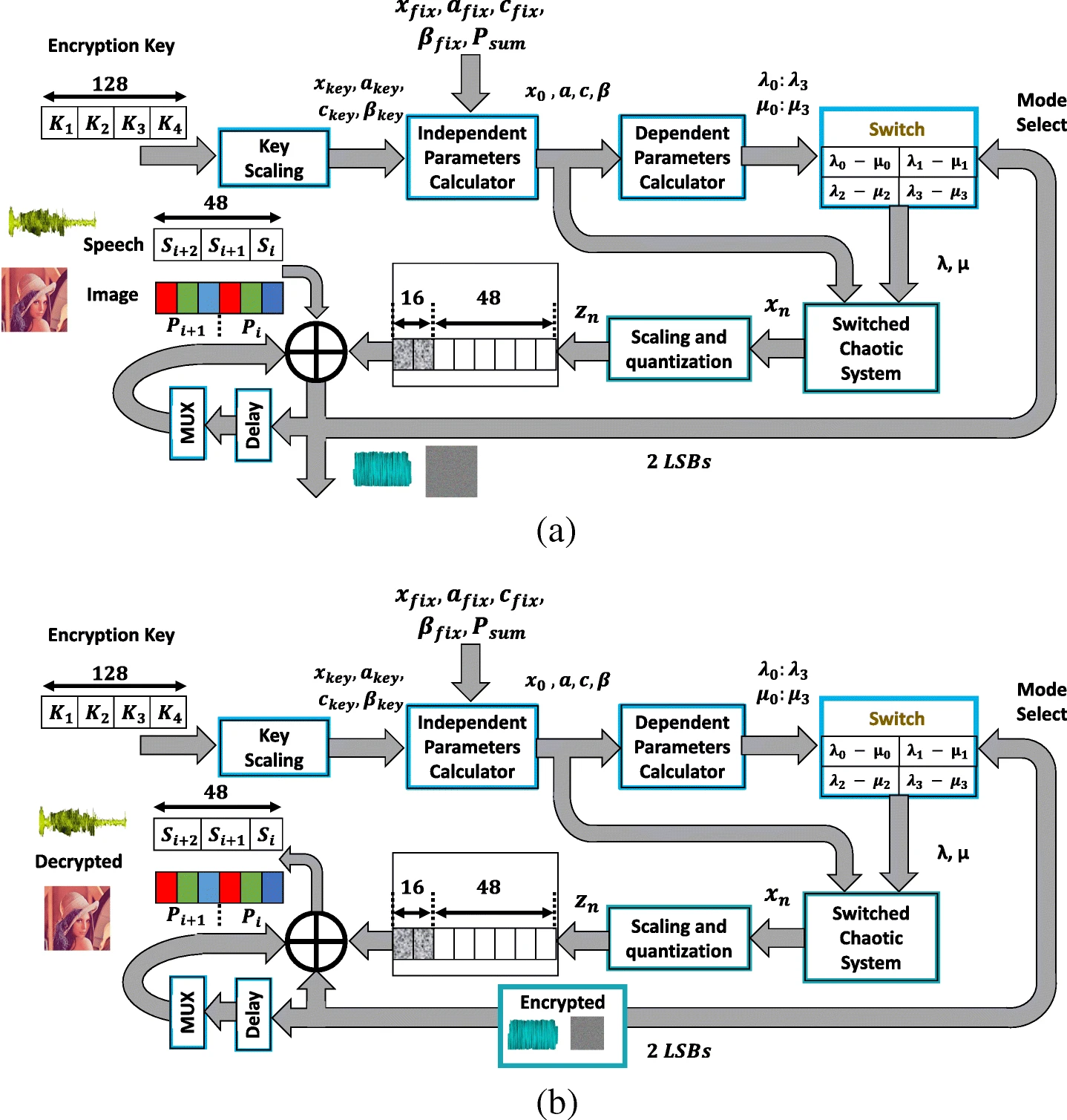
This paper presents a multi-mode generalized modified transition chaotic map and a switched chaotic encryption scheme based on it. Eight different modes of operation can be selected based on the map graph (concave or convex), the range modification procedure (shrinking or widening) and the sign of one of its independent parameters. The generalization and modification preserve the controllability and continuous chaotic behavior properties, respectively. For the same encryption key and map equation, multi-mode operation occurs through switching between four alternatives of the dependent
Novel permutation measures for image encryption algorithms
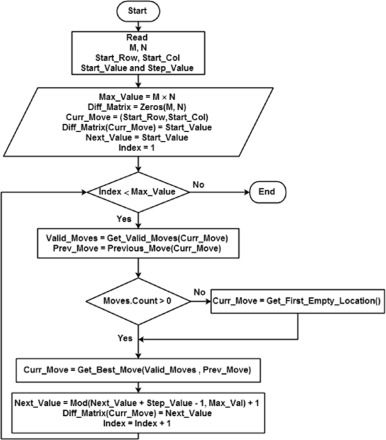
This paper proposes two measures for the evaluation of permutation techniques used in image encryption. First, a general mathematical framework for describing the permutation phase used in image encryption is presented. Using this framework, six different permutation techniques, based on chaotic and non-chaotic generators, are described. The two new measures are, then, introduced to evaluate the effectiveness of permutation techniques. These measures are (1) Percentage of Adjacent Pixels Count (PAPC) and (2) Distance Between Adjacent Pixels (DBAP). The proposed measures are used to evaluate
Novel radio frequency energy harvesting model
Energy and Environment, both are the main concern for every researcher allover the world. Alternative energy sources that are environmental friendly became the challenge to satisfy world needs. Oil and Gas are no more the main source of Energy, consequently the demand of an everlasting cheap source of energy that is environmental friendly, is the main goal recently. During the last decade, power consumption has decreased opening the field for energy harvesting to become a real time solution for providing different sources of electrical power. Energy Harvesting is a new technology that is going
A study on coexistence of different types of synchronization between different dimensional fractional chaotic systems
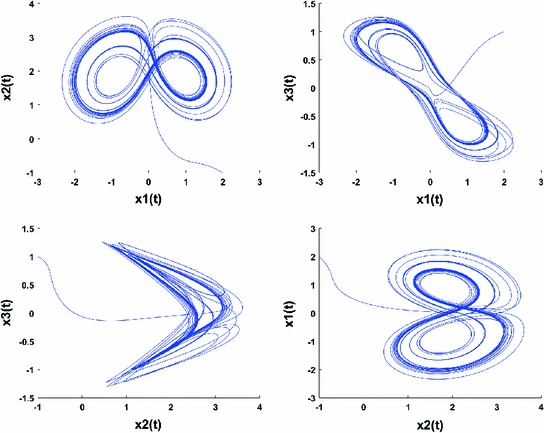
In this study, robust approaches are proposed to investigate the problem of the coexistence of various types of synchronization between different dimensional fractional chaotic systems. Based on stability theory of linear fractional order systems, the co-existence of full state hybrid function projective synchronization (FSHFPS), inverse generalized synchronization (IGS), inverse full state hybrid projective synchronization (IFSHPS) and generalized synchronization (GS) is demonstrated. Using integer-order Lyapunov stability theory and fractional Lyapunov method, the co-existence of FSHFPS
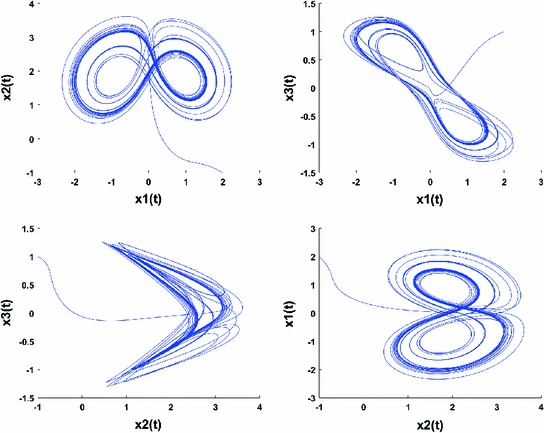
A study on coexistence of different types of synchronization between different dimensional fractional chaotic systems
In this study, robust approaches are proposed to investigate the problem of the coexistence of various types of synchronization between different dimensional fractional chaotic systems. Based on stability theory of linear fractional order systems, the co-existence of full state hybrid function projective synchronization (FSHFPS), inverse generalized synchronization (IGS), inverse full state hybrid projective synchronization (IFSHPS) and generalized synchronization (GS) is demonstrated. Using integer-order Lyapunov stability theory and fractional Lyapunov method, the co-existence of FSHFPS
Develop TE/TM Pass Filters on double-loaded-on-ridge Structure with ITO/TiN for Upstream FTTH Optical Access Networks
In this paper, TE/TM pass filters are introduced as a dual optical multiplexer in the fiber-to-the home (FTTH) uplink transmission. The architecture is implemented at 1330 nm wavelength, with a double-loaded-on-ridge structure. In the TE pass filter, TM mode couples with plasmonic mode while TE mode is guided through the core with low losses due to the effect of the two plasmonic materials. The TM mode is directed through the heart, though, in the TM pass filter. Transparent conductive oxides (TCOs) as Indium Tin Oxide (ITO), in addition to Titanium Nitride (TiN) are proposed as plasmonic
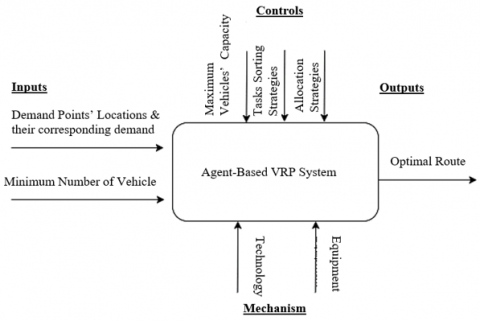
Modelling of agent-based vehicle routing problem using unified modelling language
The Vehicle Routing Problem (VRP) is among the most studied optimization problems in the field of supply chain management. Typically, VRP requires dispatching a fleet of vehicles from a central depot to deliver demand to pre-determined spatially dispersed customers, with the objective of minimizing the total routing cost, and the constraint of not exceeding vehicles' capacities. Agent Based Modelling (ABM) assists industries in the use of technology to support their decision-making process. This paper proposes a model of an Agent Based Vehicle Routing Problem System. The system under study is

Modelling of Crime Record Management System Using Unified Modeling Language
Crime records management is a system that helps police keep records of citizens’ complaints files, investigation evidence and processes. In addition, it helps police keep records of the criminals who have been arrested or who are to be arrested. This paper aims to model the Crime Record Management System (CRMS) using various Unified Modeling Language (UML) diagrams, to demonstrate an explicit visualization of the system. Also, showing the communication among different actors, and the sequence of activities and interactions. The perspective of modeling the CRMS is by covering four stages, which
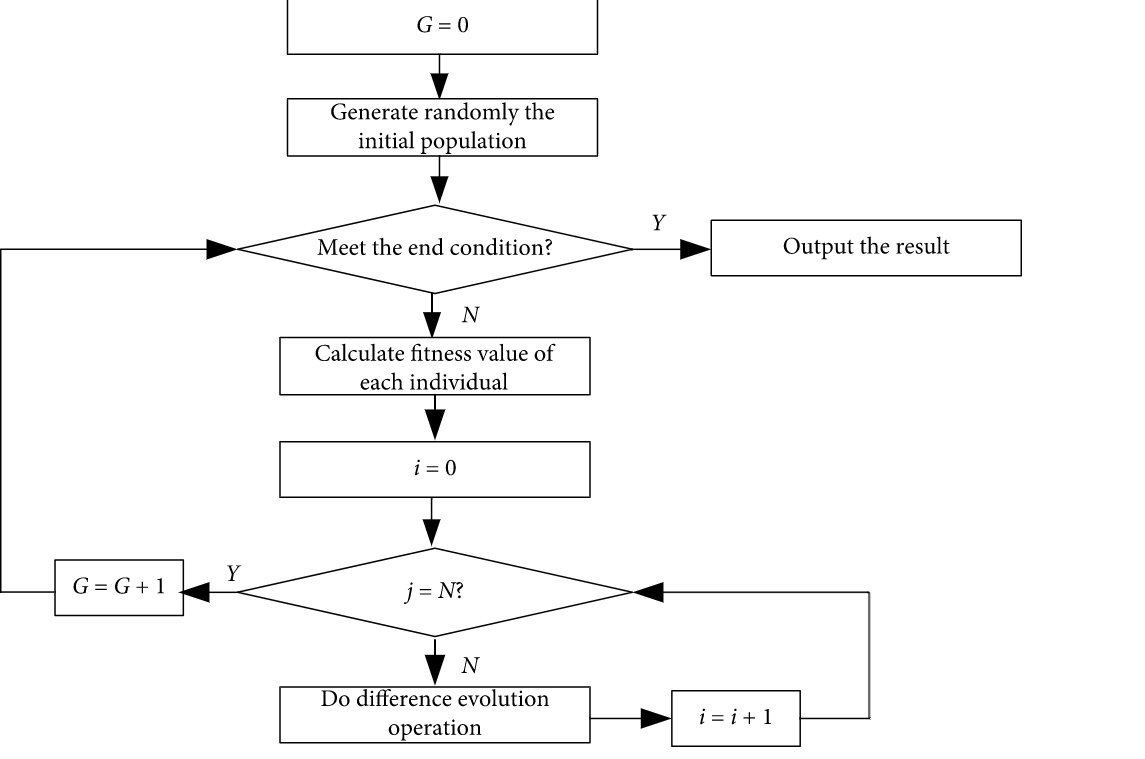
Enhanced Success History Adaptive de for Parameter Optimization of Photovoltaic Models
In the past few decades, a lot of optimization methods have been applied in estimating the parameter of photovoltaic (PV) models and obtained better results, but these methods still have some deficiencies, such as higher time complexity and poor stability. To tackle these problems, an enhanced success history adaptive DE with greedy mutation strategy (EBLSHADE) is employed to optimize parameters of PV models to propose a parameter optimization method in this paper. In the EBLSHADE, the linear population size reduction strategy is used to gradually reduce population to improve the search
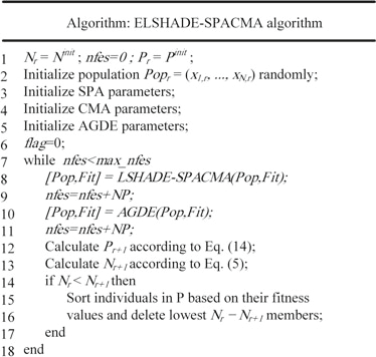
Single-Objective Real-Parameter Optimization: Enhanced LSHADE-SPACMA Algorithm
Real parameter optimization is one of the active research fields during the last decade. The performance of LSHADE-SPACMA was competitive in IEEE CEC’2017 competition on Single Objective Bound Constrained Real-Parameter Single Objective Optimization. Besides, it was ranked fourth among twelve papers were presented on and compared to this new benchmark problems. In this work, an improved version named ELSHADE-SPACMA is introduced. In LSHADE-SPACMA, p value that controls the greediness of the mutation strategy is constant. While in ELSHADE-SPACMA, p value is dynamic. Larger value of p will
Pagination
- Previous page ‹‹
- Page 17
- Next page ››
