A fully automated approach for Arabic slang lexicon extraction from microblogs
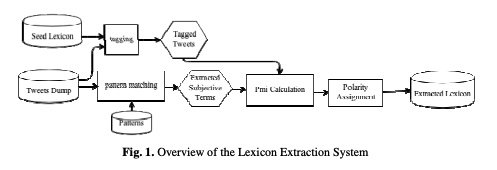
With the rapid increase in the volume of Arabic opinionated posts on different social media forums, comes an increased demand for Arabic sentiment analysis tools and resources. Social media posts, especially those made by the younger generation, are usually written using colloquial Arabic and include a lot of slang, many of which evolves over time. While some work has been carried out to build modern standard Arabic sentiment lexicons, these need to be supplemented with dialectical terms and continuously updated with slang. This paper proposes a fully automated approach for building a
AraVec: A set of Arabic Word Embedding Models for use in Arabic NLP
Advancements in neural networks have led to developments in fields like computer vision, speech recognition and natural language processing (NLP). One of the most influential recent developments in NLP is the use of word embeddings, where words are represented as vectors in a continuous space, capturing many syntactic and semantic relations among them. AraVec is a pre-Trained distributed word representation (word embedding) open source project which aims to provide the Arabic NLP research community with free to use and powerful word embedding models. The first version of AraVec provides six
Strain correction in interleaved strain-encoded (SENC) cardiac MR
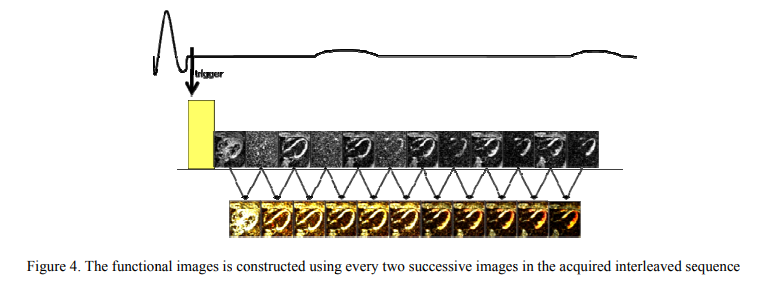
The strain encoding (SENC) technique directly encodes regional strain of the heart into the acquired MR images and produces two images with two different tunings so that longitudinal strain, on the short-axis view, or circumferential strain on the long-axis view, are measured. Interleaving acquisition is used to shorten the acquisition time of the two tuned images by 50%, but it suffers from errors in the strain calculations due to inter-tunings motion of the heart. In this work, we propose a method to correct for the inter-tunings motion by estimating the motion-induced shift in the spatial
Ambient and wearable sensing for gait classification in pervasive healthcare environments
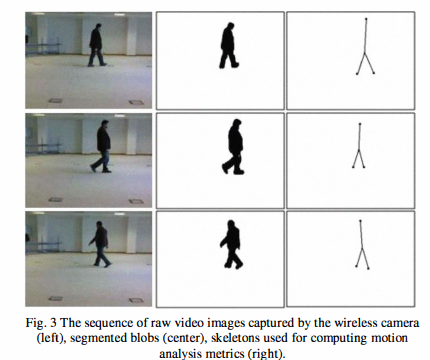
Pervasive healthcare environments provide an effective solution for monitoring the wellbeing of the elderly where the general trend of an increasingly ageing population has placed significant burdens on current healthcare systems. An important pervasive healthcare system functionality is patient motion analysis where gait information can be used to detect walking behavior abnormalities that may indicate the onset of adverse health problems, for quantifying post-operative recovery, and to observe the progression of neurodegenerative diseases. The development of accurate motion analysis models
Janitor, certificate and jury (JCJ): Trust scheme for wireless ad-hoc networks
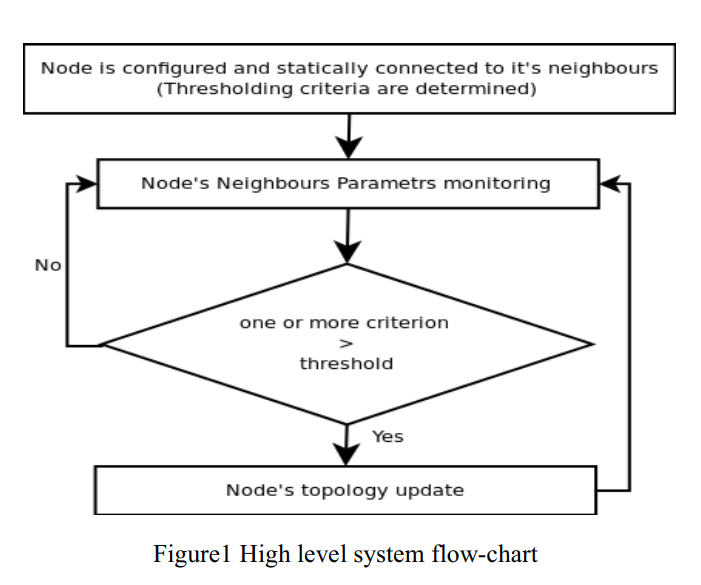
Ad hoc networks are peer mobile nodes that self configure to form a network. In these types of networks there is no routing infrastructure, and usually nodes have limited resources. This imposes a serious problem due to some nodes' selfishness and willingness to preserve their resources. Many approaches have been proposed to deal with this problem and mitigate the selfishness; amongst these approaches are reputation systems. This paper proposes a reputation system scheme that helps isolating misbehaving nodes and decreasing their ability to launch an attack on the network. The idea of this
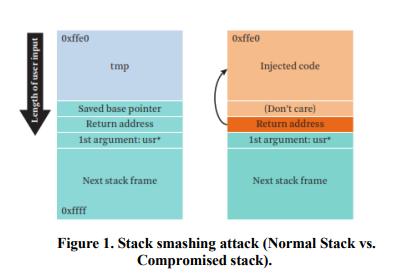
Survey of Code Reuse Attacks and Comparison of Mitigation Techniques
Code-Reuse Attacks (CRAs) are solid mechanisms to bypass advanced software and hardware defenses. Due to vulnerabilities found in software which allows attackers to corrupt the memory space of the vulnerable software to modify maliciously the contents of the memory; hence controlling the software to be able to run arbitrary code. The CRAs defenses either prevents the attacker from reading program code, controlling program memory space directly or indirectly through the usage of pointers. This paper provides a thorough evaluation of the current mitigation techniques against CRAs with regards to
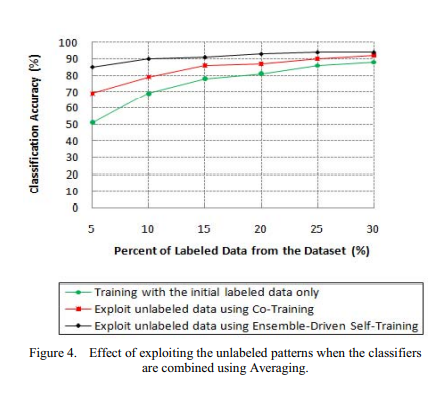
A semi-supervised learning approach for soft labeled data
In some machine learning applications using soft labels is more useful and informative than crisp labels. Soft labels indicate the degree of membership of the training data to the given classes. Often only a small number of labeled data is available while unlabeled data is abundant. Therefore, it is important to make use of unlabeled data. In this paper we propose an approach for Fuzzy-Input Fuzzy-Output classification in which the classifier can learn with soft-labeled data and can also produce degree of belongingness to classes as an output for each pattern. Particularly, we investigate the
Replica placement in peer-assisted clouds: An economic approach
We introduce NileStore, a replica placement algorithm based on an economical model for use in Peer-assisted cloud storage. The algorithm uses storage and bandwidth resources of peers to offload the cloud provider's resources. We formulate the placement problem as a linear task assignment problem where the aim is to minimize time needed for file replicas to reach a certain desired threshold. Using simulation, We reduce the probability of a file being served from the provider's servers by more than 97.5% under realistic network conditions. © 2011 IFIP International Federation for Information
Cloud-based parallel suffix array construction based on MPI
Massive amount of genomics data are being produced nowadays by Next Generation Sequencing machines. The suffix array is currently the best choice for indexing genomics data, because of its efficiency and large number of applications. In this paper, we address the problem of constructing the suffix array on computer cluster in the cloud. We present a solution that automates the establishment of a computer cluster in a cloud and automatically constructs the suffix array in a distributed fashion over the cluster nodes. This has the advantage of encapsulating all set-up details and execution of
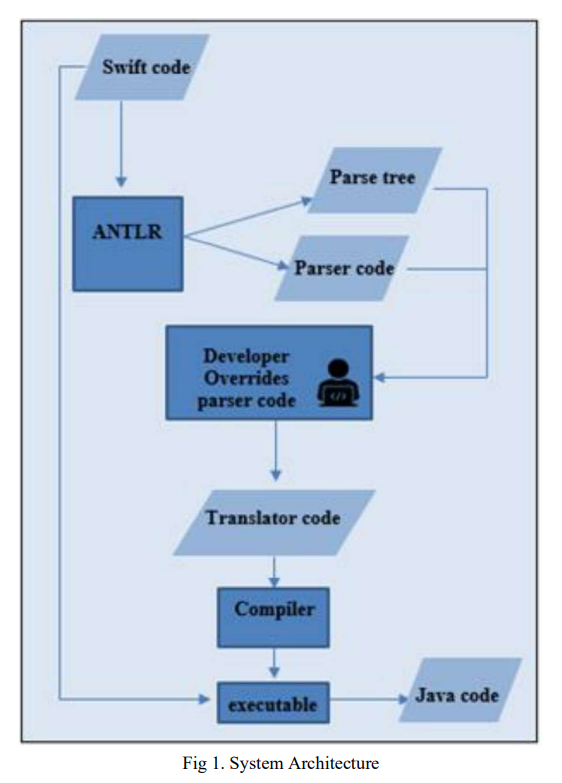
Trans-Compiler based Mobile Applications code converter: Swift to java
Numerous commercial tools like Xamarin, React Native and PhoneGap utilize the concept of cross-platform mobile applications development that builds applications once and runs it everywhere opposed to native mobile app development that writes in a specific programming language for every platform. These commercial tools are not very efficient for native developers as mobile applications must be written in specific language and they need the usage of specific frameworks. In this paper, a suggested approach in TCAIOSC tool to convert mobile applications from Android to iOS is used to develop the
Pagination
- Previous page ‹‹
- Page 26
- Next page ››
